5 Ways to Prevent PC from WannaCry Ransomware on Windows 10, 8.1, 8, 7, Vista, XP
Jun. 23, 2022 / Updated by Helia to Windows Driver Solutions
The WannaCry ransomware quite makes the Windows users “wanna cry” those days. Since the WannaCry cyberattack occurred in the afternoon of Friday, May 12th, 2017, the ransomware attacks have continued to spread over hundreds and thousands of organizations, individuals in more than 150 countries, just like what you watch in the movie Resident Evil. Generally, infected PC can be in no WiFi/network connection, blue screen of death, black screen, etc. However, the malware has now damaged a host of computers and caused system crashes and a huge loss in organizations including schools, hospitals, banks, airports, etc. Computer owners who suffer the cyber-attack were asked for a “$300 worth of bitcoins” ransom payment for the decrypt or the data recovery. For example, the upcoming Disney work Pirates of the Caribbean: Dead Men Tell No Tales has been stolen for ransom and the hackers have threatened to release the first 5 minutes of the film until the ransom is paid. But in fact, those who have sent the payment fail to get the decryption on their Windows computer.

The EternalBlue exploit, developed by the NSA, is known to be used by the WannaCry ransomware worm to attack the Windows OS, especially the older Windows editions like Windows 7, Windows Vista, Windows XP and the predecessors. Due to the weak support by the Redmond giant, such operating systems are too vulnerable to be prevented from the WannaCry ransomware. While the Kill Switch measure has slowed the malware spread by accident, the variations, Wanna Decrypt0r 2.0, WannaSister.exe or so, have spread on a scale without control.
Updated News: In the June, new vaiation of the ransomware, Petya, has attacked European contries like Britain, Ukraine and more. Petya makes use of all the Windows vulnerabilities, which are also made used by WannaCry (related to the patch MS17-010) on May 12th and the variations (related to patches CVE-2017-8543 and cve-2017-8464) on June 23rd. Once Petya attacks Windows users computer, it will directly encrypt the hard drive disk without notice. When users reboot the PC, they won't see the Windows desktop but the ransom payment screen.

It’s frustrated to see the smug “Ooops” and bitcoins payment message on the screen. (BITCOINS? Amazing idea.) But if you’re now the lucky dog surviving from the “Resident Evil on the Internet”, it’s important to take immediate actions to prevent your Microsoft Windows computers from the WannaCry ransomware attack.
See Also:How to Avoid Ransomware Attacking Your Windows, iOS or Android Device
How to Avoid the WannaCry Ransomware Attacking Your Windows Computers
Don't Wanna Cry! We’ve had some simple and effective methods for you to keep your desktop or laptop away from the malware. You may like to check out the following workarounds for your data security:
Way 1. Keep Good Habits on Using Your Computer
Most of the computer virus infections are caused by the bad computer using habits, such as clicking on suspicious links or e-mails, using the simple passwords, never scanning the computer, seldom updating drivers, etc. Thus could make your laptop or desktop in lower security levels and infect the WannaCry ransomware easily. So from now on, do the following:
1. Avoid clicking on suspicious links and e-mails.
2. Enable the Windows Defender as well as the Windows Firewall, and adjust the Internet settings to higher security levels.
3. Enable the automatic Windows updates or regularly install Windows security patch released by Microsoft.
4. Regularly backup your important data like documents, photos and more.
5. Install anti-virus programs for extra security.
These are the easy methods for a basic protection.
Way 2. Disable the TCP Ports 445, 135, 138, etc. to Prevent the WannaCry Ransomware
For Windows 7 and the later Windows OS like Windows Vista, Windows XP, Windows 2000, etc., it’s necessary to close the ports 445, 135, 138, 139 and prevent from the malware on the Windows 10, 8.1, 8, 7, Vista, XP or so, because computers are easy to be held to ransom if there are opening ports like that, especially when the ports are in LISTENING status. You can do a port scan to the internal IP to see if the ports are open:
1. Open Command Prompt in your Windows computer.
2. Type netstat –na.
3. Hit the Enter.
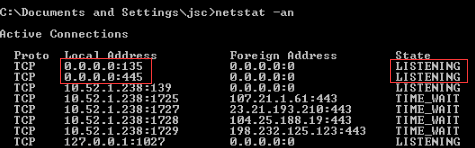
If you find the 135, 445 and 139 are on and in LISTENING, you can disable the TCP ports via the 3 methods below:
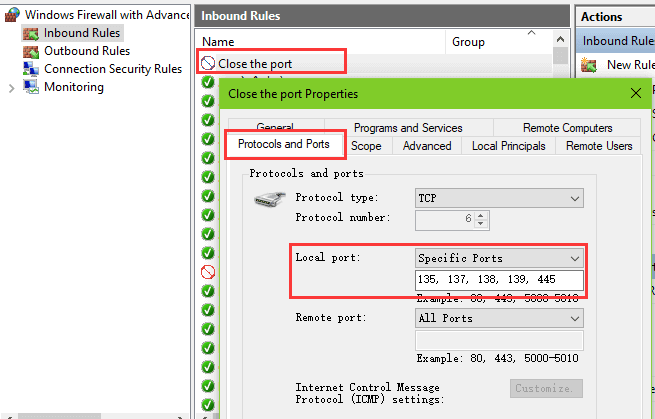
Disable Port 445, 135, 138, 139, etc. via the Firewall
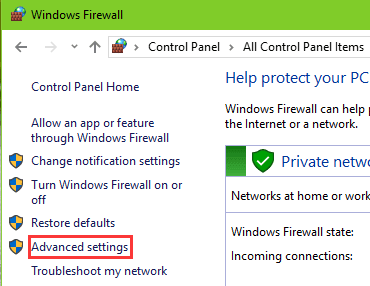
1. Open the Control Panel.
2. Click the Windows Firewall.
3. Click Advanced settings.
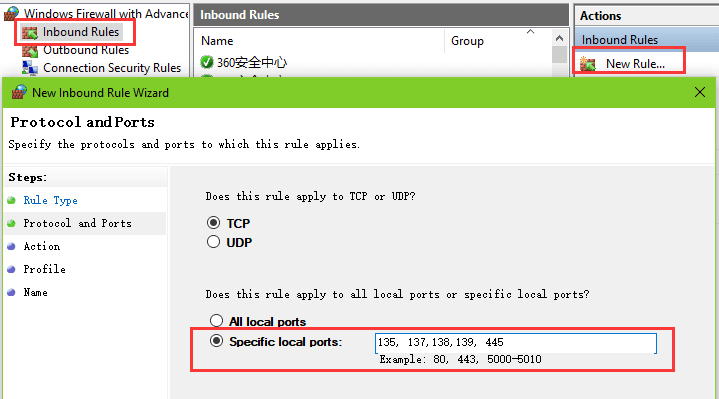
4. Click Inbound Rule.
5. On the right side, click New rule.
6. Chose the Port.
7. Click Next.
8. Choose Specific local ports.
9. Type 135, 137,138,139, 445.
10. Click Next.
11. Choose Block the connection.
12. Click Next.
13. Tick the three checkboxes and click Next.
14. Type Close the port into the Name box.
15. Click Finish.
Then you can verify the ports by double-clicking the rule you’ve created just now.
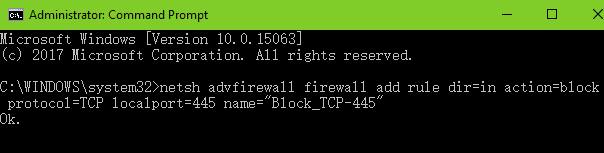
Disable Port 445, 135, 138, 139, etc. through Command Lines
Open the Command Prompt and then type the following command lines into the box to disable them:
netsh advfirewall set allprofile state on
netsh advfirewall firewall add rule dir=in action=block protocol=TCP localport=445 name="Block_TCP-445"
netsh advfirewall firewall add rule dir=in action=block protocol=TCP localport=135 name="Block_TCP-135"
netsh advfirewall firewall add rule dir=in action=block protocol=TCP localport=138 name="Block_TCP-138"
netsh advfirewall firewall add rule dir=in action=block protocol=TCP localport=139 name="Block_TCP-139"
Disable Port 445, 135, 138, 139, etc. by Modifying the Registry
Also, modifying the registry to prevent the WannaCry malware is available.
1. Use Windows shortcut keysWin + R to launch the Run.
2. Type regedit and press the Enter.
3. Expand the entries via the path: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\NetBT\Parameters. (Note: For Windows 10 Creators Update users, you can paste it directly into the bar and press the Enter.)
4. In the subkey Parameters, right click the blank area for New.
5. Select the DWORD (32-bit) Value or the QWORD (64-bit) Value. (Note: Make sure your system type via Win + PauseBreak and choose the corresponding one.)
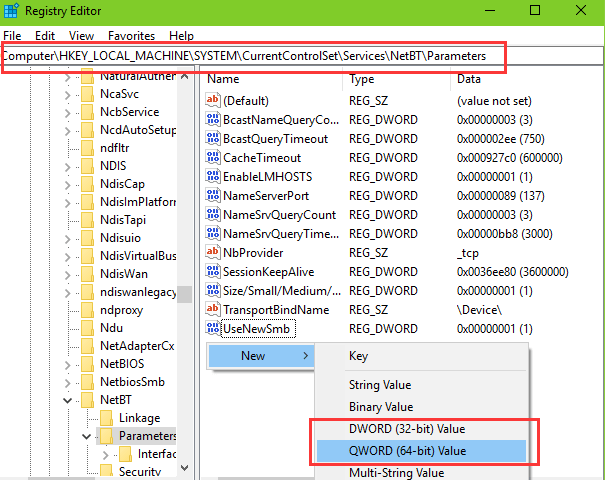
6. Rename the New Value #1 you created to SMBDeviceEnabled.
7. Double-click the SMBDeviceEnabled.
8. Change the Value data to 0.
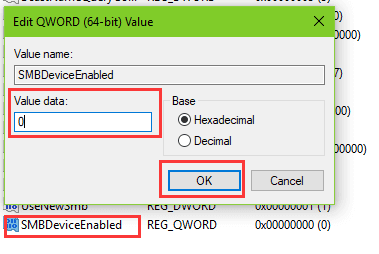
Note: You can’t be more careful when modifying the Registry because it is a sensitive Windows database and if there are issues with the registry, you may encounter other serious system problems. So it is better to back up the Registry before you modify it.
To keep a double-security computer, you still need to disable the TCP ports one by one with the methods in the posts below:
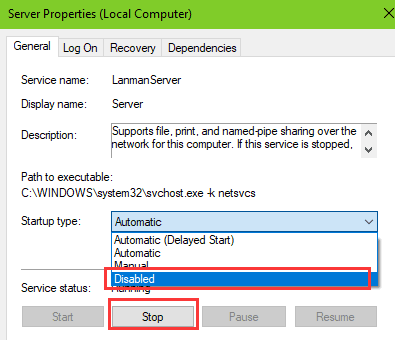
Way 3. Disable Services to Protect Your Windows Computer from the Cyberattack
Besides disabling the TCP port, it is necessary to disable the Server if you are using a Windows 7 laptop or desktop.
2. Navigate to the Server service and double-click it.
3. Select the Disable from the drop-down menu of the Startup type.
4. Click the Stop button.
5. Click Apply and OK.
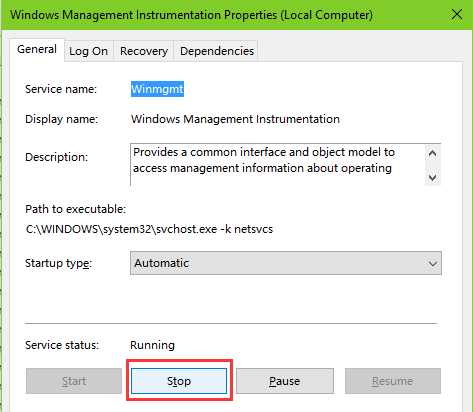
Also, you need to disable the Windows Management Instrumentation service.
1. Navigate to the WMI service and double-click it.
2. Click the Stop button.
3. Click OK.
To get a double-safety Windows, it is better to disable the TCP ports one by one again and avoid the WannaCry worm attack.
Way 4. Install the Windows Security Patch to Prevent the WannaCry Ransomware
You can also download the security patches to set a high-security level and protect the computer data. Microsoft has released the special security patches for Windows XP and WindowsServer2003 on May 13th. Besides, for Windows 7 users, you can install the MS17-010 patch to prevent the WannaCrypt worm.
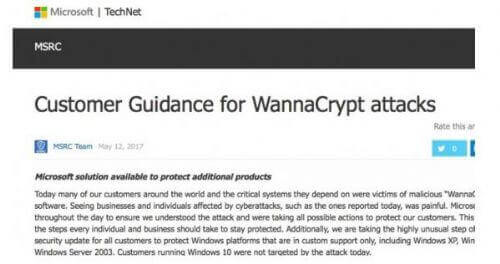
The patch downloads link is available below:
Patch for Windows XP and WindowsServer2003/English language security updates: http://download.windowsupdate.com/d/csa/csa/secu/2017/02/windowsserver2003-kb4012598-x64-custom-enu_f24d8723f246145524b9030e4752c96430981211.exe
Patch for Windows 7: https://technet.microsoft.com/zh-cn/library/security/MS17-010.aspx
You can download the patches from a Mac and transfer them with a new USB drive to your computer in the Safe Mode and then install them.
Updated News: On June 13th, 2017, Microsoft released new patches CVE-2017-8543 and CVE-2017-8464 to prevent the attack. The patches is available on Microsoft official site: https://support.microsoft.com/en-us/help/4025687/microsoft-security-advisory-4025685-guidance-for-older-platforms
See Also:How to Enter Safe Mode in Windows 10, 8.1, 8, 7, Vista, XP
Way 5. Create a System Restore Point to Backup and Protect Your Data
It is important to backup the files like hardware device drivers, photos, applications, etc. on your computer. A system restore point is also necessary. There is a one-click solution, Driver Talent, to backup the drivers and the OS. It is a professional driver and system backup utility and it offers all the previous driver versions you’ve backed up to restore to.
Click the button above to get this utility and follow the steps to back up the drivers or create a system restore point.
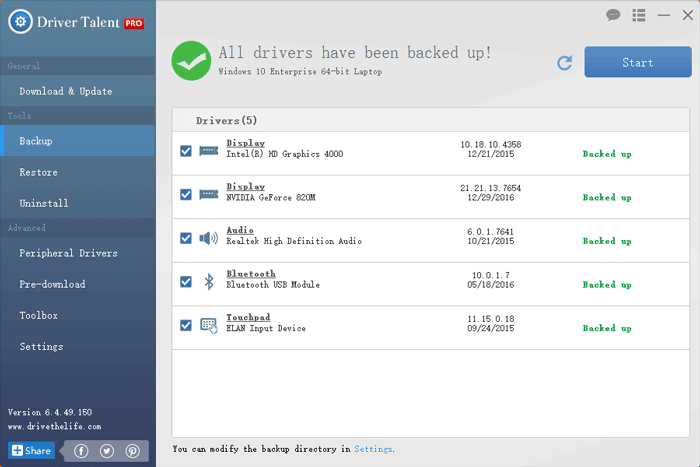
1. Launch Driver Talent and click on Scan to enter the Backup menu.
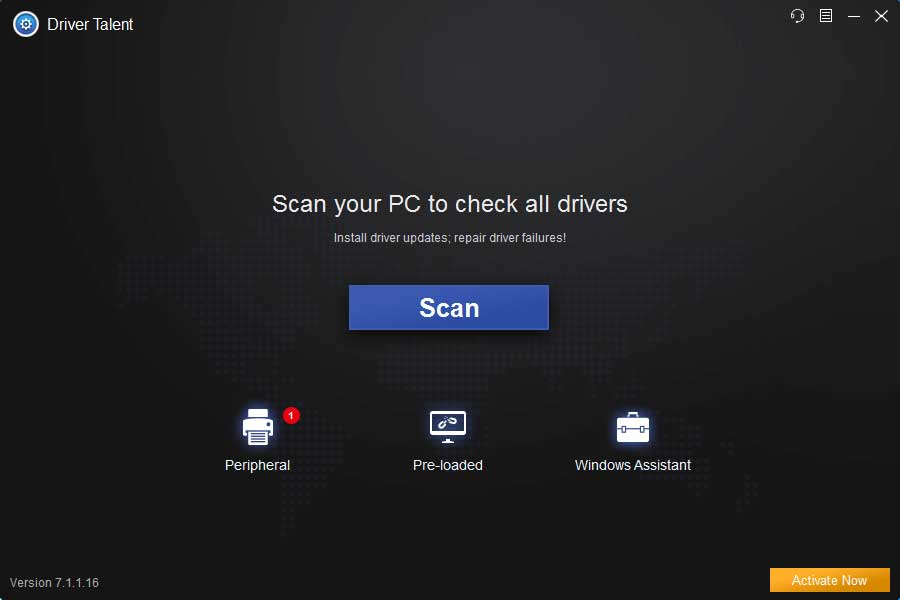
2. Select the drivers you want to backup and click the Start.
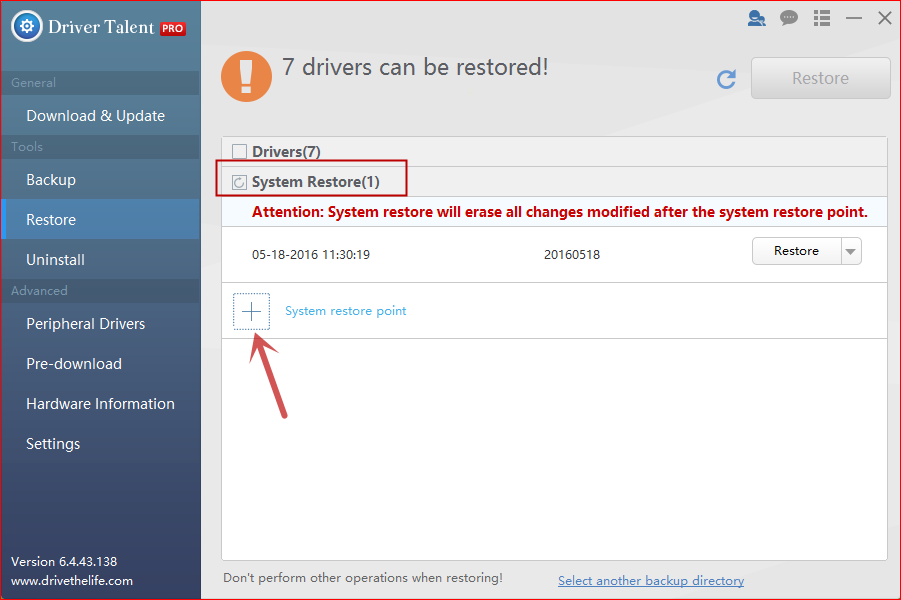
3. Select Restore menu and select System Restore tab on the right.
4. Click System restore point and name the point.
5. Click Create to create a restore point.
See Also:How to Use System Restore to Fix Windows 10 Issues
That’s it. All of above are possible the best solutions to prevent your Windows laptop or desktop from WannaCry ransomware attack. You can comment below or go to the OSToto official forum to discuss the issue if you encounter any WannaCry problem.

|
ExplorerMax |

|
Driver Talent for Network Card | |
| Smart and advanced file explorer tool for Windows platforms | Download & Install Network Drivers without Internet Connection | |||
| 30-day Free Trial | Free Download |