The WannaCry ransomware makes many Windows users learn about the TCP ports, like port 135, port 139, port 445, etc. The Remote Procedure Call (RPC) port 135 is used in client or server apps and other Windows XP/Windows 2000 programs. If you allow remote users to get into your network through VPN, you need to open the 135 port to make the access to the Exchange server available. The RPC makes it possible for the programs on your computer to run the code on a remote computer, and virus takes advantage of this to infect your computer. For example, in 2003, MSBlaster, the computer worm developed by an 18-year-old boy, makes use of the exploits in RPC to attack a flood of Windows computers.

The EternalBlue WannaCry virus can utilize the RPC exploits and affect the port 135 between the RPC and the DCOM and then infect your Windows machine. Most of the users may prevent the Windows computers from the WannaCry ransomware via disabling the TCP ports 135 in the Windows Firewall. It’s one of the fastest workarounds to manually close the ports through the Control Panel, but for a double-safety Windows, it is recommended to close the port 135, 137, 139, 445, etc. one by one.
See Also:
Disable Port 139 and Avoid WannaCry Ransomware on Windows 10, 8.1, 8, 7, Vista, XP
How to Avoid Ransomware Attacking Your Windows, iOS or Android Device
How to Disable TCP Port 135 on Your Windows Computer
You can follow the steps below to backup the system data, check the port status and close the port 135 on your Microsoft Windows 10/8.1/8/7/Vista/XP/2000.
Step 1. Create a System Restore Point for the Windows
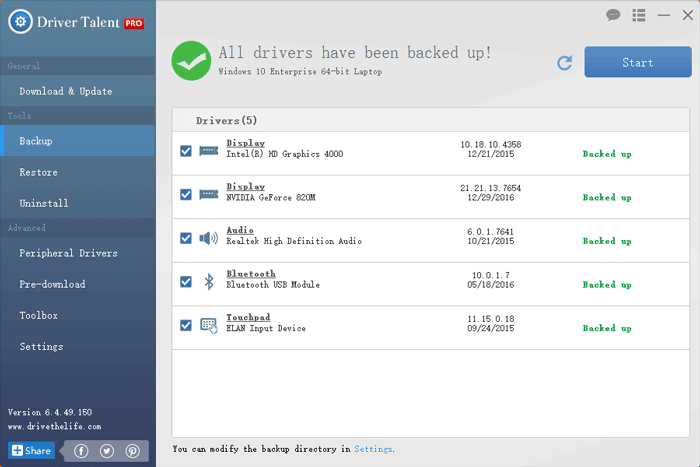
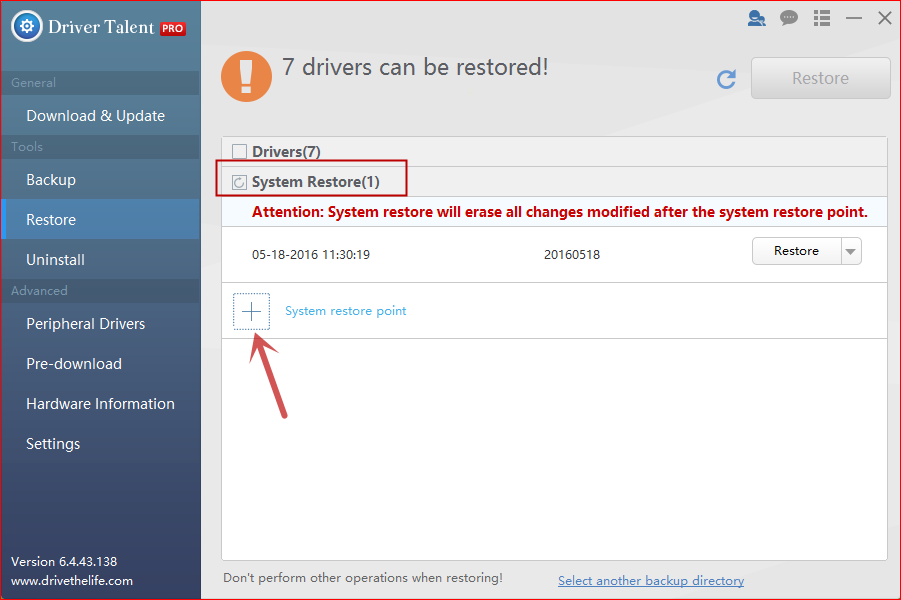
Before any system changes, it is important to back up important data such as vital system files, windows drivers, photos and more. in case you encounter problems like blue screen, mouse and keyboard not working, error 0x8000ffff, etc. System restore is used to roll back the PC's state to that of a previous point in time. You can use Driver Talent to backup hardware device drivers and create a system restore point.
1. Go to the Backup menu on Driver Talent and select the drivers you want to backup. Click the Start.
2. Go to the Restore menu and select the System Restore tab. Click System restore point and name it.
3. Click Create to create a restore point.
See Also:How to Use System Restore to Fix Windows 10 Issues
Step 2. Check If the TCP Port 135 Is in LISTENING Status
1. Launch the Command Prompt on the Windows. (Note: Win 10/8/7/Vista users can do a search for the Command Prompt directly, and Win XP users can go to the All programs in the Start menu for it.)
2. Type netstat –na into the box.
3. Press the key Enter.
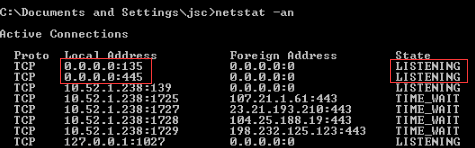
If the 135 port is in LISTENING status, go to step 3 to close it again.
Step 3. Close the Port 135
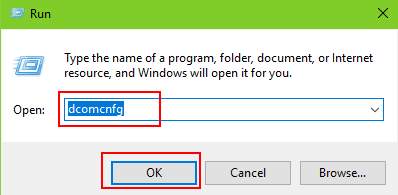
1. Use Windows shortcut keysWin + R to launch the Run.
2. Type into dcomcnfg.
3. Hit the Enter.
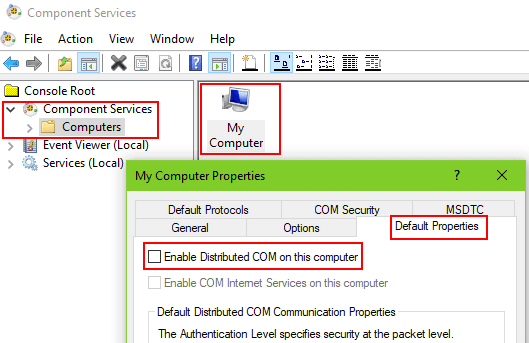
4. Expand the Component Services.
5. Highlight the Computers.
6. Right click the My Computer on the middle side.
7. Select the Properties.
8. Choose the Default Properties tab.
9. Uncheck the Enable Distributed COM on this computer.
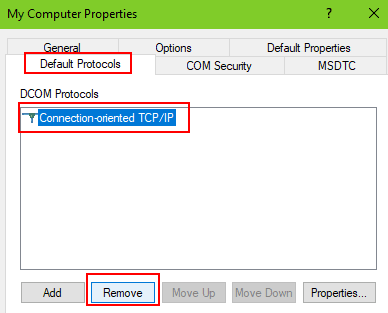
10. Choose the Default Protocols.
11. Highlight the Connection-oriented TCP/IP under the DCOM Protocols.
12. Click the Remove button.
13. Click the Apply.
14. Click the OK.
15. Restart the computer.
Now you’ve closed the TCP port 135 extra and your computer is in double-safety status away from the WannaCry ransomware attack.
See Also:5 Ways to Prevent PC from WannaCry Ransomware on Windows 10, 8.1, 8, 7, Vista, XP
Hope you stop “Wanna Cry” and your Windows computer is in the high-security level before related organizations offer effective solutions to kill the cyber attack. If you have any other questions about how to disable TCP port 135 or close other high-risk ports to prevent the EternalBlue worm, please comment below or go to the OSToto official forum for help.